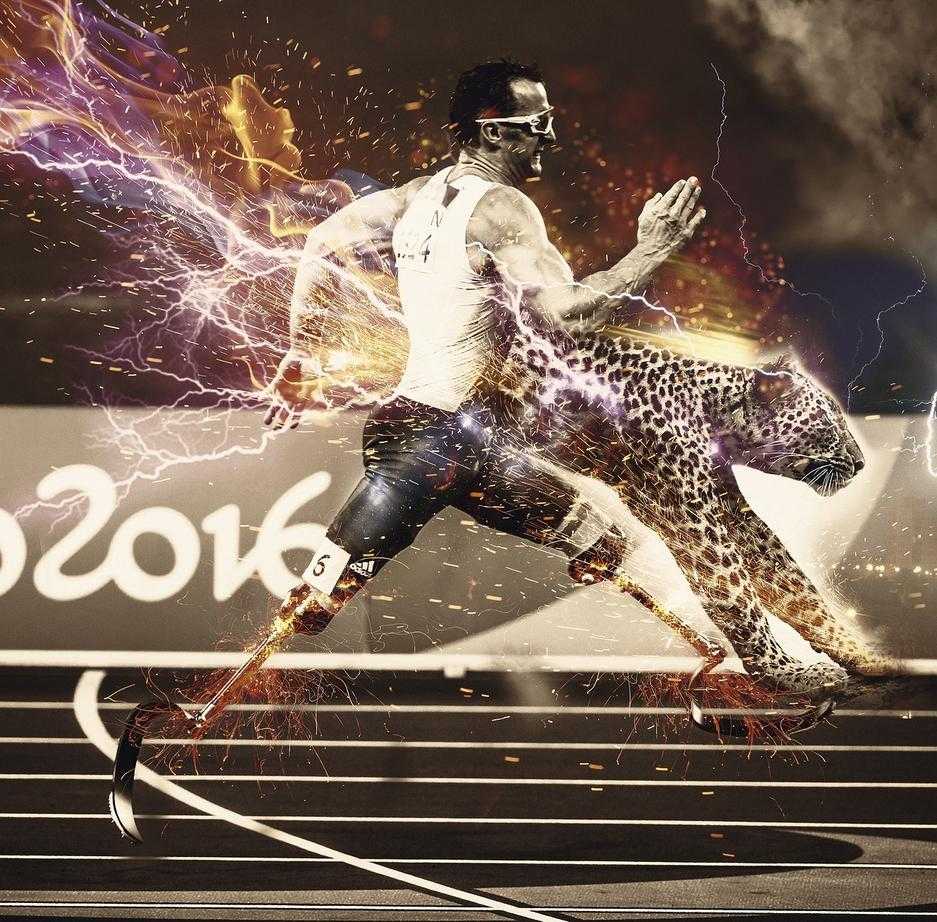
Technology is evolving at a pace that makes yesterday’s breakthrough feel outdated by tomorrow. If you’re here, you’re likely looking for clear, reliable insights into the latest developments shaping tech—from AI advancements and cybersecurity strategies to practical gadget hacks that actually make a difference. This article is designed to cut through the noise and deliver focused, actionable information aligned with what you’re searching for.
We analyze emerging innovations, break down complex concepts into practical takeaways, and reference current industry research and real-world applications to ensure accuracy and relevance. Whether you’re exploring new AI tools, strengthening your security posture with endpoint detection and response, or staying ahead of digital transformation trends, you’ll find grounded explanations backed by expert analysis.
By the end, you’ll have a clearer understanding of what’s changing, why it matters, and how to apply these insights confidently in your own tech decisions.
Traditional antivirus software used to be enough. Install it, run scans, block known malware—done. But today’s attackers don’t knock on the front door. They slip in through phishing emails, zero-day exploits (previously unknown software flaws), and stolen credentials. In other words, they bypass prevention entirely.
So what’s the real problem? Security teams often lack visibility after a device is compromised. Once an attacker lands on a laptop or server, they move laterally, escalate privileges, and quietly extract data. Prevention alone can’t answer the critical question: what’s happening right now?
That’s where a proactive model comes in. Instead of only blocking threats, organizations now deploy endpoint detection and response to continuously monitor activity, analyze behavior, and surface anomalies in real time.
What should you look for next?
- Continuous monitoring capabilities
- Behavioral analytics
- Automated containment features
In the following sections, we’ll break down the technology, strategy, and practical steps required to detect and respond to threats directly at the network endpoint level.
What is Endpoint Detection and Response (EDR)?
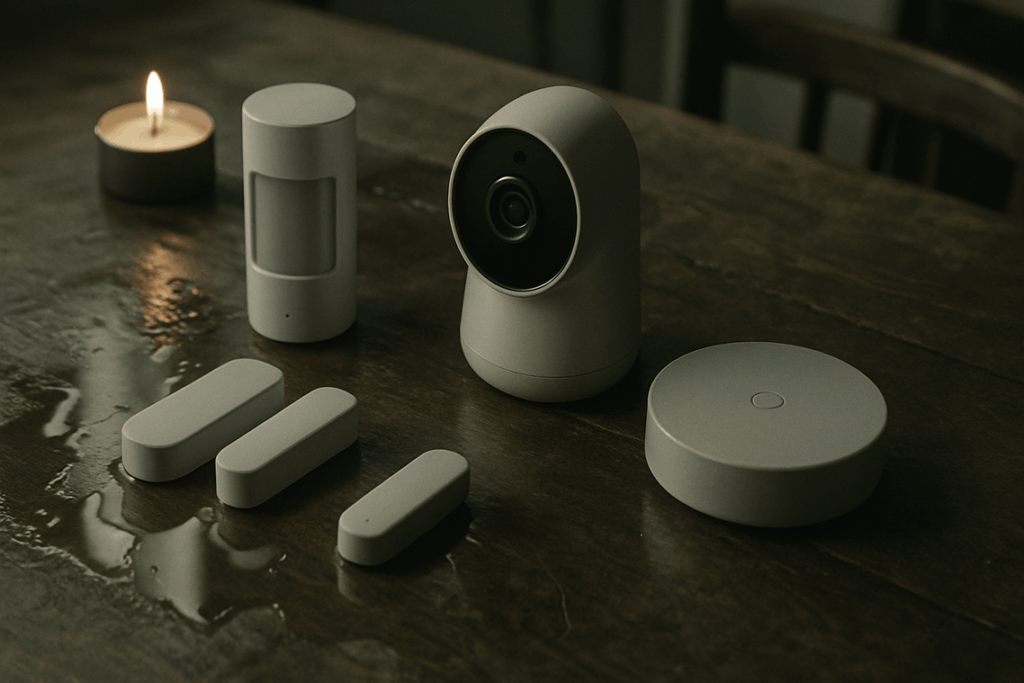
At its core, endpoint detection and response is an integrated cybersecurity solution that continuously monitors devices—like laptops, servers, and mobile phones—for suspicious activity. An endpoint simply means any device connected to a network. EDR tools collect real-time data from these endpoints, analyze behavior patterns, and trigger automated actions when something looks wrong. Think of it as a system that not only watches but also reacts.
To make this clearer, consider the difference between antivirus and EDR. Traditional antivirus is like a security guard holding a list of known criminals. If someone matches the list, they’re stopped. EDR, on the other hand, acts more like a detective roaming the building, spotting unusual behavior—like someone trying every locked door—even if they’ve never been seen before.
The primary objectives are straightforward. First, detect security incidents as they happen. Next, contain threats at the device level to prevent spread. Then investigate scope and root cause (the original trigger of an attack). Finally, provide remediation guidance so teams can fix vulnerabilities.
Looking ahead, experts speculate EDR will evolve with AI-driven behavioral baselines and predictive threat hunting (think Minority Report, minus the sci-fi drama). As threats grow stealthier, proactive detection will likely become the standard rather than the upgrade.
How Proactive Endpoint Monitoring Works: A Technical Breakdown

Proactive endpoint monitoring starts with data collection. Lightweight agents are installed on laptops, servers, and mobile devices. These agents quietly record telemetry—meaning continuous streams of system activity data—such as process execution (which programs are running), registry modifications (changes to core system settings), network connections, and file alterations. Think of it as a security camera for your device, except it watches behavior instead of hallways.
Next, that telemetry is streamed in real time to a centralized platform. Here’s where things get interesting. Using machine learning (algorithms that improve by analyzing patterns), behavioral analysis (detecting deviations from normal activity), and threat intelligence feeds (databases of known malicious indicators), the system flags suspicious behavior known as Indicators of Compromise, or IoCs. For example, if a legitimate tool suddenly starts making unusual outbound connections at 3 a.m., that’s a red flag. (Even your laptop shouldn’t be pulling all-nighters.)
Finally, the “response” kicks in. In a mature endpoint detection and response system, automated actions can isolate an infected device, terminate malicious processes, or block harmful traffic—stopping lateral movement before it spreads across the network. Pro tip: automation reduces response time from hours to seconds.
Essential Features of a Modern Endpoint Security Platform
Threat Hunting Capabilities
First and foremost, modern platforms must empower proactive defense. Threat hunting refers to the process where analysts actively search endpoint data for hidden threats that automated tools may overlook. According to IBM’s Cost of a Data Breach Report (2023), organizations that extensively use security AI and automation detect breaches 108 days faster on average. That time difference can mean millions saved. While some argue automated alerts are sufficient, real-world breaches—like SolarWinds—show attackers often dwell undetected for months. Proactive hunting closes that gap.
Behavioral Analytics and AI
Traditional signature-based detection relies on known malware patterns. However, zero-day threats (previously unseen exploits) don’t have signatures yet. Behavioral analytics uses AI to flag anomalies—such as unusual login times or privilege escalation attempts. Gartner notes that behavior-based tools significantly reduce false negatives compared to legacy antivirus. In other words, it’s less about matching fingerprints and more about spotting suspicious behavior (think less “wanted poster,” more “body language expert”).
Forensics and Investigation Tools
Equally important, strong forensics features provide a detailed attack timeline—how entry occurred, what systems were accessed, and how lateral movement unfolded. This visibility supports compliance and aligns with a structured cybersecurity risk assessment step by step framework.
Integration with SIEM and SOAR
Finally, seamless integration with SIEM and SOAR tools strengthens endpoint detection and response by unifying alerts, automating remediation, and reducing response times across the entire security ecosystem.
Implementing Your Proactive Endpoint Security Strategy
A few years ago, I walked into a network audit convinced everything was covered—until we discovered three forgotten laptops quietly syncing data from a former contractor. That moment taught me the first rule: you can’t protect what you can’t see.
Step 1: Asset Inventory. Start by identifying every endpoint—laptops, desktops, servers, mobile devices, even IoT gadgets. An endpoint is simply any device that connects to your network. Build a living inventory, not a one-time spreadsheet (trust me, it will age fast).
Next, move carefully.
Step 2: Phased Rollout. Pilot your endpoint detection and response tools with a small group. Test policies, monitor workflows, and gather feedback before scaling.
Then refine.
Step 3: Policy Configuration and Tuning. Detection rules must be calibrated to reduce false positives—alerts that flag harmless activity.
Finally, practice.
Step 4: Training and Incident Response Drills. Run simulations so your team reacts confidently, not chaotically, when real alerts hit.
Building a resilient, future-proof security posture starts with clarity. In simple terms, a proactive approach means watching your systems continuously and reacting in real time, not after headlines break. That is where endpoint detection and response comes in: software that monitors devices, records suspicious behavior, and enables rapid containment.
However, blocking attacks alone is not enough. Threat actors evolve, and eventually something slips through. The real risk is lacking visibility when it does.
Therefore, by adopting this mindset, organizations shift from passive defense to active threat hunting, strengthening their overall security framework (see this practical overview: https://example.com). Stay vigilant always.
Stay Ahead of Emerging Threats and Innovations
You came here looking for clarity on today’s fast-moving tech landscape — from AI breakthroughs to evolving cybersecurity risks — and now you have a sharper understanding of what’s changing and why it matters. More importantly, you can see how gaps in protection, outdated tools, and reactive strategies leave systems exposed when speed and precision matter most.
The reality is simple: innovation moves fast, and attackers move faster. Without strong endpoint detection and response, proactive monitoring, and smart adoption of new technologies, vulnerabilities grow quietly until they become costly problems.
Now it’s time to act. Audit your current tech stack. Strengthen your security framework. Leverage proven tools and trusted insights to stay ahead instead of scrambling to catch up.
Don’t wait for a breach or missed opportunity to force your next move. Take control now, upgrade your defenses, and position yourself at the forefront of innovation — because the safest and smartest systems are built before they’re tested.