The traditional firewall is no longer enough. As remote work, cloud platforms, and increasingly sophisticated cyber threats redefine the digital landscape, perimeter-based security has become a liability rather than a safeguard. This article explores how to design a modern network built on verified trust, where identity replaces location as the core security boundary. Drawing on years of cybersecurity breach analysis and real-world implementation of advanced defense strategies, this guide outlines the principles, technologies, and practical steps behind zero trust architecture. You’ll gain a clear roadmap for enforcing strict access controls and building a resilient, identity-first security framework.
The Flaw in the Fortress: Why Perimeter Security is Obsolete
For decades, cybersecurity followed the “castle-and-moat” model—a hardened external firewall guarding a trusted internal network. Once inside the walls, users and devices were assumed safe. It worked when systems were centralized and employees sat inside the same building. But that world no longer exists.
Research from Verizon’s 2023 Data Breach Investigations Report found that 74% of breaches involved the human element, including stolen credentials and insider misuse. That statistic alone exposes the flaw: attackers don’t need to break the wall if they can walk through the front gate.
Critical Weaknesses Exposed
- Insider Threats: Employees or contractors may intentionally—or accidentally—leak data. Think of the 2017 NSA contractor breach, where classified tools were removed from secure systems.
- Compromised Credentials: According to IBM, stolen credentials were the most common initial attack vector in 2023, averaging $4.62 million per breach.
- The Dissolving Edge: Cloud apps, IoT devices, and remote work have erased the “inside vs. outside” boundary.
| Traditional Model | Modern Reality |
|——————-|—————-|
| Fixed perimeter | Distributed cloud services |
| Trusted internal users | Identity constantly verified |
| On-site workforce | Remote and hybrid teams |
Security now demands zero trust architecture—continuous verification, not blind trust. For implementation details, see a practical guide to implementing the nist cybersecurity framework.
The Zero Trust Mandate: Core Principles of Identity-First Security

Back in 2019, when large-scale supply chain attacks began dominating headlines, many organizations realized perimeter-based security was no longer enough. That shift accelerated after 2020’s rapid move to remote work. Since then, zero trust architecture has moved from buzzword to baseline strategy.
Principle 1: Never Trust, Always Verify
First and foremost, no user or device is trusted by default. Authentication (verifying identity) and authorization (verifying permissions) must happen every single time access is requested. Even if someone logs in from the office network, verification still applies. Think of it like airport security: having a ticket doesn’t mean you skip screening (nice try, though).
Principle 2: Enforce Least Privilege Access
Next, organizations apply least privilege access, meaning users receive only the minimum permissions required to do their jobs.
- Finance can access billing systems
- Developers can access code repositories
- HR can access employee records
Nothing more. If an attacker compromises one account, the blast radius stays small. Pro tip: Review permissions quarterly; roles change faster than you think.
Principle 3: Assume Breach
Rather than hoping defenses hold, modern security assumes an attacker may already be inside. This mindset gained traction after major breaches in the early 2020s revealed months-long dwell times (IBM reports the average breach lifecycle remains over 200 days). Detection and containment become priorities.
Principle 4: Implement Micro-segmentation
Finally, micro-segmentation divides networks into isolated zones. Internal firewalls restrict lateral movement, so one compromised system cannot freely access another. In practice, this means tighter controls around sensitive databases and critical applications.
Admittedly, critics argue this model increases complexity and slows productivity. However, after years of escalating ransomware attacks, layered verification is no longer optional—it’s strategic resilience.
Building a verified-access network is not about adding more tools — it’s about aligning the right technology stack to guarantee that only the right people access the right resources. The payoff? Fewer breaches, lower operational risk, and smoother user experiences (yes, security can feel invisible when it’s done right).
Identity and Access Management (IAM) forms the backbone. Single Sign-On (SSO) lets users authenticate once and securely access multiple applications, reducing password fatigue and helpdesk tickets. Multi-Factor Authentication (MFA) adds an extra proof of identity—like a mobile push or biometric scan—dramatically lowering takeover risks (Microsoft reports MFA blocks over 99.9% of automated attacks [Microsoft]). Centralized identity providers (IdPs) unify oversight, giving teams visibility and control from one dashboard.
Privileged Access Management (PAM) protects high-level accounts such as administrators. These accounts are prime targets because they unlock critical systems. PAM vaults credentials, enforces just-in-time access, and records sessions, so if something goes wrong, you have a forensic trail. The benefit is containment: even if attackers get in, they can’t roam freely.
Software-Defined Perimeter (SDP) takes this further by creating dynamic, one-to-one encrypted connections between a verified user and a specific resource. The broader network stays dark to outsiders, aligning with zero trust architecture principles. That invisibility shrinks your attack surface dramatically.
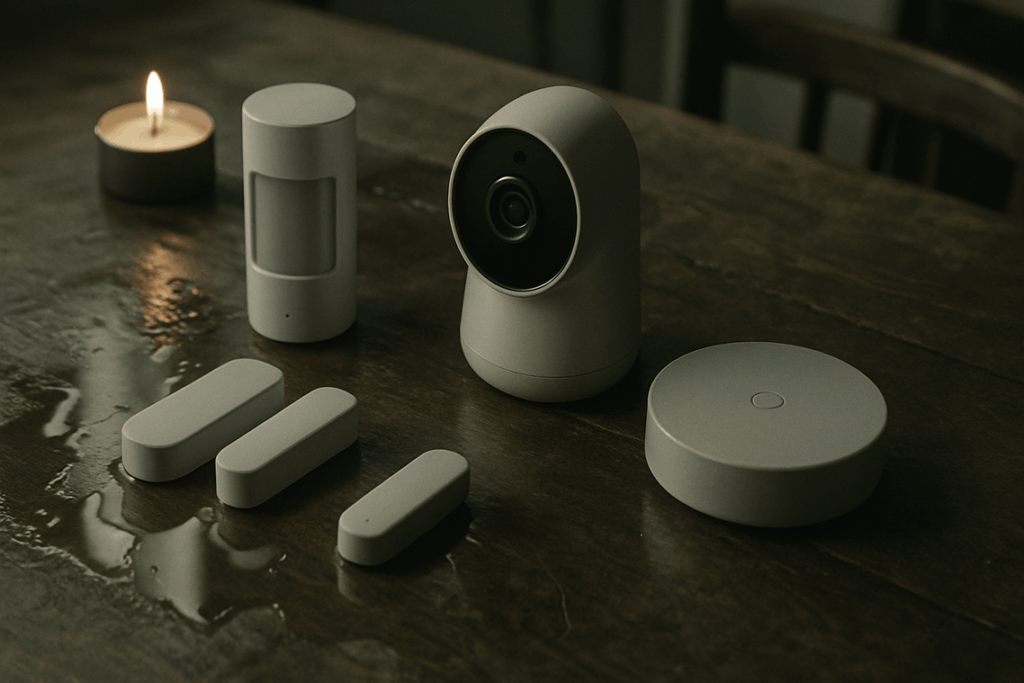
Finally, Enhanced Endpoint Security validates device health before granting access. Compliance checks—patch levels, encryption, active threat protection—ensure only trusted machines connect. Pro tip: automate posture checks to avoid bottlenecks. The result is confident, scalable, and resilient access for enterprises.
A Practical Roadmap for Implementation
Step 1: Discover and Define Protect Surfaces
Start by identifying your most critical DAAS—data, applications, assets, and services. A protect surface is the smallest unit of value that must be secured (think customer databases, payment systems, or proprietary code). Unlike a broad attack surface, this approach narrows focus. Admittedly, deciding what’s “most critical” isn’t always obvious. When in doubt, ask: what would hurt most if exposed?
Step 2: Map Transaction Flows
Next, document how users, devices, and systems interact with those protect surfaces. This means tracing legitimate traffic patterns (who accesses what, when, and how). Some teams underestimate this step, yet unclear flow mapping often leads to broken policies later.
Step 3: Architect the Network
Using principles like micro-segmentation and tools such as SDP (Software-Defined Perimeter), build controls around verified flows. This is where zero trust architecture becomes actionable.
Step 4: Monitor and Maintain
Finally, continuously log, analyze, and refine. Threats evolve—and honestly, so should your policies.
Building a Resilient, Proactive Defense
The era of implicit trust in networking is over, and clinging to outdated perimeter defenses leaves your organization exposed. A resilient future demands explicit identity verification at every access point through zero trust architecture.
If you’re serious about closing security gaps and stopping breaches before they start, now is the time to assess your framework, implement identity-first controls, and strengthen your defenses today.